Stay Ahead: Don't Overlook Vulnerabilities
Protect your digital assets with our proactive Bug Bounty platform. Identify vulnerabilities before they become threats.
It takes a hacker to know a hacker
Bug bounty programs allow hackers to help you find application defects that elude conventional security tools and teams.
Trained to see what others miss
Gain a fresh perspective so you don’t miss flaws that malicious actors can exploit.
Continuous testing, constant protection
Keep watchful eyes on your applications, cloud assets, APIs, and supply chain at all times.
Access expert skills
Access technical skills your team lacks to be sure security doesn’t slow down the pace of innovation.
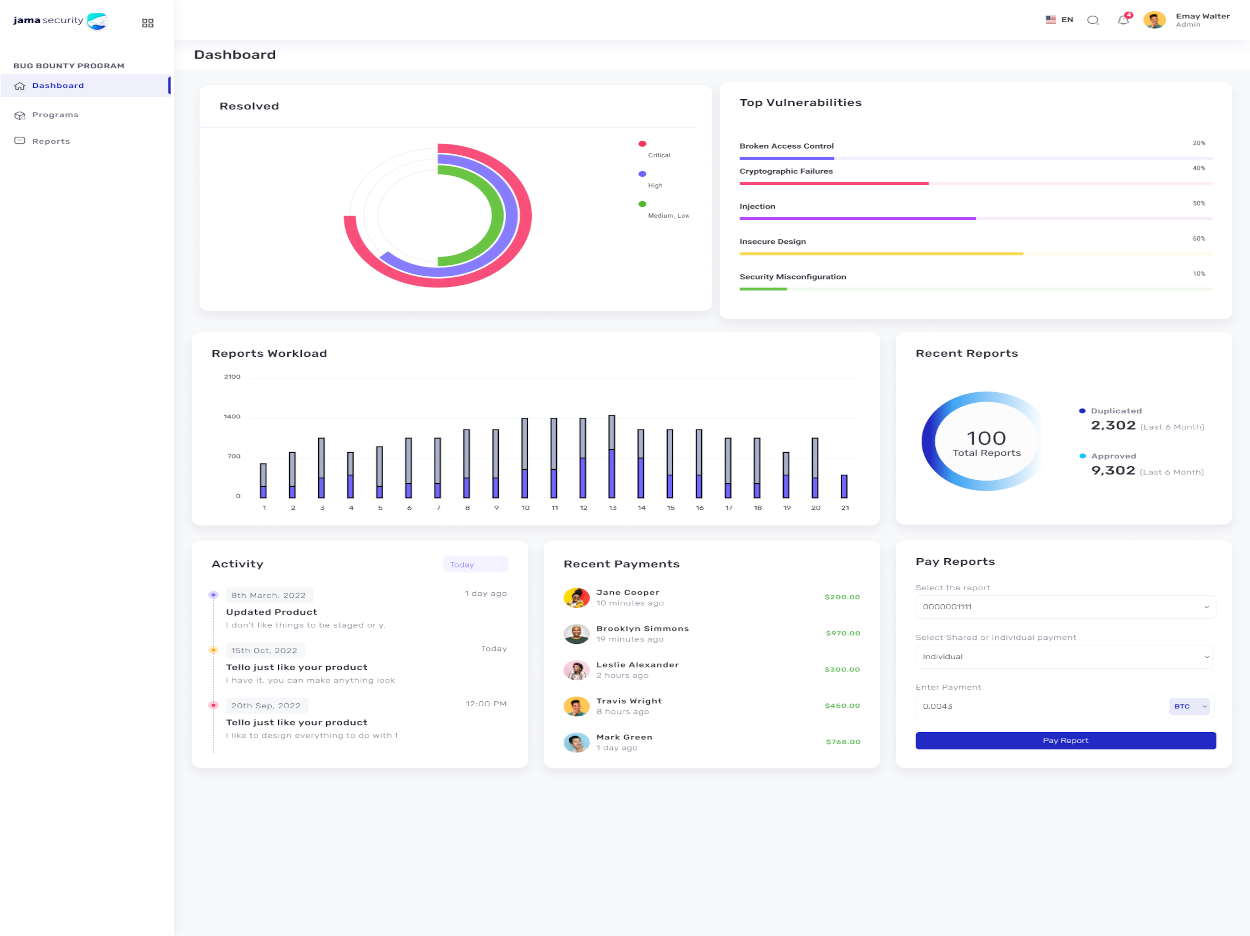
Features
Powerful Advanced Features
Experience our Bug Bounty platform's arsenal of cutting-edge tools and capabilities designed to enhance your cybersecurity defenses. Unleash the power of advanced security features.
Measuring Bug Bounty Success
Implementing a Bug Bounty program provides valuable metrics and insights that gauge the effectiveness of your security efforts. These metrics go beyond traditional security measures, offering a comprehensive view of your organization's cybersecurity posture.
Vulnerability Discovery Metrics
Our Bug Bounty platform provides you with precise metrics on the number and types of vulnerabilities discovered. You gain insights into the most common weaknesses, enabling targeted security enhancements.
Remediation Speed and Efficiency
Track the time it takes to remediate reported vulnerabilities with our Bug Bounty platform. These metrics help you assess the effectiveness of your response processes and ensure swift issue resolution.
Hunter Performance Analytics
Gain insights into the performance of ethical hackers in your Bug Bounty program. Evaluate their accuracy, collaboration, and contribution to your organization's cybersecurity. Identify top performers and nurture lasting partnerships.
Comprehensive Report Assessment
Our Bug Bounty platform offers a thorough assessment of submitted reports. Our team of experts meticulously reviews and validates findings, providing you with actionable insights and recommendations for effective vulnerability resolution.
- Thorough Validation
- Expert Evaluation
- Actionable Insights
- Precise Findings
- Efficient Resolution
- Reliable Reporting
- Expert Recommendations
- Holistic Assessment
Advanced Features
Exploring Advanced Capabilities
Implementing a Bug Bounty program provides valuable metrics and insights that gauge the effectiveness of your security efforts. These metrics go beyond traditional security measures, offering a comprehensive view of your organization's cybersecurity posture.
Threat Simulation Testing
Our Bug Bounty platform offers advanced threat simulation testing. This feature allows you to emulate real-world cyberattacks to assess your organization's readiness and response capabilities. By simulating various attack scenarios, you can proactively strengthen your defenses and ensure optimal incident response.
Continuous Monitoring and Alerting
With our Bug Bounty platform, you benefit from continuous monitoring and real-time alerting. This feature ensures that any unusual or suspicious activities are detected promptly. By receiving instant alerts, you can take immediate action to investigate and mitigate potential threats, maintaining the security of your digital assets 24/7.
Process
Bug Bounty Process
Explore the steps to bug bounty success.
Scope Definition
Identify program goals and targets.
Vulnerability Discovery
Ethical hackers uncover security weaknesses.
Report Submission
Hunters submit findings for assessment.
Remediation & Rewards
Resolve issues and reward contributions.
Around-the-Clock Assistance
Comprehensive Support
We take pride in offering responsive and knowledgeable support to address your inquiries and provide solutions promptly. Your security and peace of mind are our top priorities, and our support team is committed to delivering the assistance you need, no matter the time or day.
Get our any Service
With Suitable Pricing
Develop advanced security strategies and innovative solutions to improve your infrastructure.
Stater
Free
- Create Program
- 1 User
- Publish Programs
- Private Programs
- Integrations
- Pre-report qualification using machine learning
- Support 24/7
- Specialized posts
Advanced
$500/month
- Create Program
- 100 Users
- Publish Programs
- Private Programs
- Integrations
- Pre-report qualification using machine learning
- Support 24/7
- Specialized posts
Premium
Contact Sales
- Create Program
- Unlimited Users
- Publish Programs
- Private Programs
- Integrations
- Pre-report qualification using machine learning
- Support 24/7
- Specialized posts